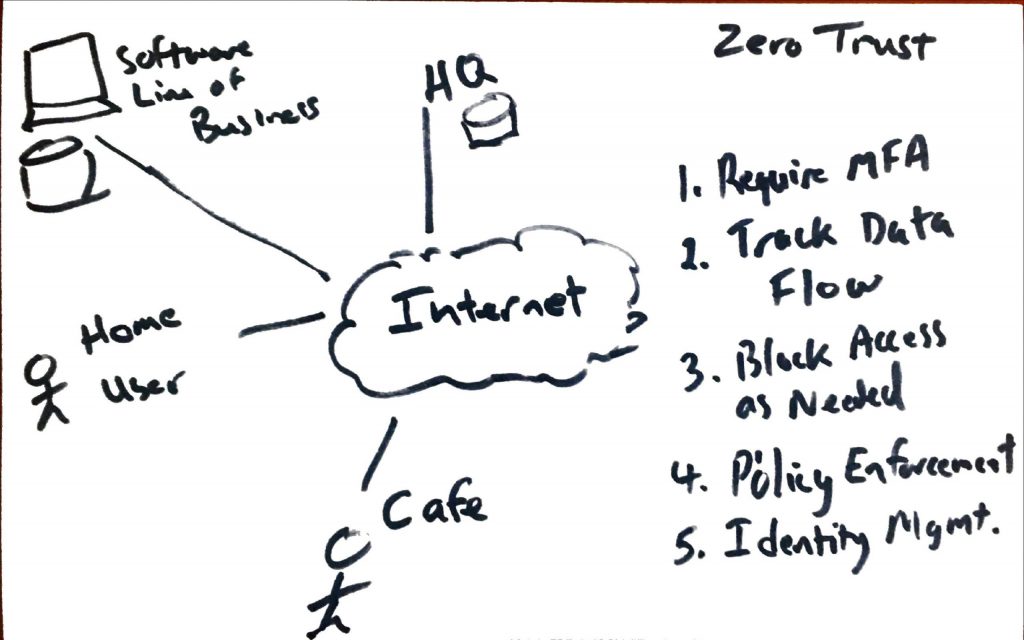
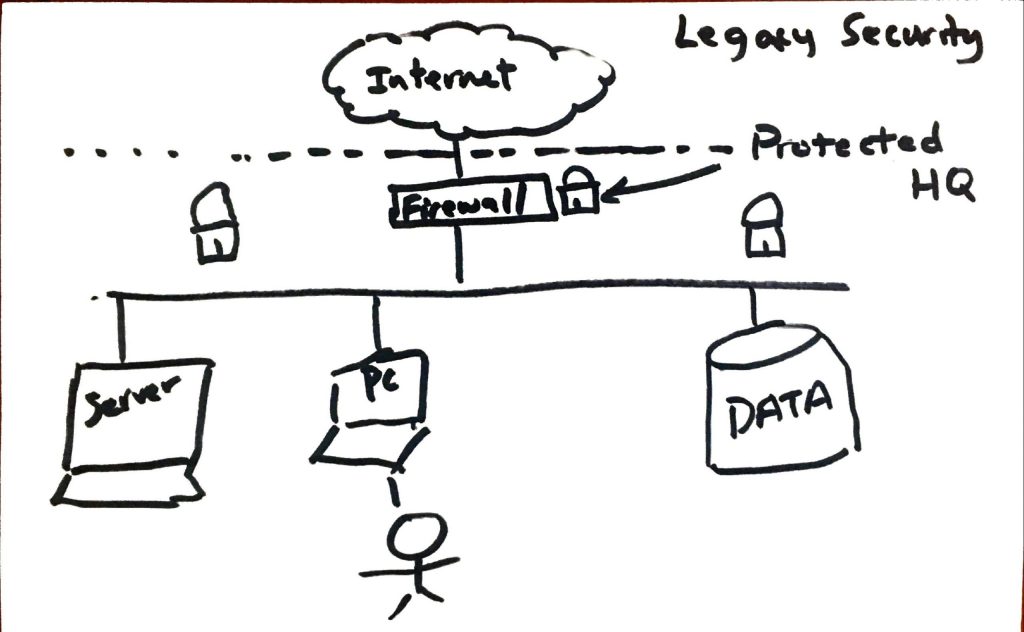
The technology landscape has changed dramatically in the last few years. Cloud adoption and the Covid19 pandemic have moved the network perimeter from company HQ to remote locations. So how are you protecting these remote locations and endpoints?
Here’s a few ways we’re doing this for clients:
- MFA using tools such as Google Authenticator, LastPass, Microsoft Authenticator, Azure Active Directory, Cisco Duo
- Microsoft 365, Google DLP, SIEM for tracking data flows
- Blocking access via traditional firewalls, Microsoft 365, Cisco Umbrella DNS, Azure
- Azure/M365 policy enforcement for exchange of data between clouds, devices, HQ
- Overall identity management to detect and block risky sign-ins or other behaviors
Video below from Checkpoint is a simple overview of the problem: