Compliance Services
CMMC 2.0, NIST CSF, and NIST 800-171 alignment for defense contractors and regulated industries.
Security-First IT Aligned with Industry Standards
We don't just provide IT support — we deliver structured, standards-based security aligned with recognized compliance frameworks. Essential for organizations working with the Department of Defense, handling Controlled Unclassified Information (CUI), or operating in regulated industries.
Our compliance services help you assess current risk, implement required controls, maintain compliance over time, and prepare for audits and certification.

CMMC 2.0
Cybersecurity Maturity Model Certification
CMMC 2.0 is the Department of Defense framework required for contractors handling Federal Contract Information (FCI) and Controlled Unclassified Information (CUI).
Level 1 — Foundational
Basic cyber hygiene, 17 practices, annual self-assessment
Level 2 — Advanced
110 controls (NIST 800-171), required for CUI handling
Level 3 — Expert
Advanced threat protection based on NIST 800-172
Gap Assessment
Comprehensive review of your current security posture against CMMC, NIST CSF, or NIST 800-171 requirements.
Control Implementation
Deploy required security controls including access management, MFA, endpoint protection, and network segmentation.
Documentation Support
System Security Plans (SSP), policies, procedures, and audit-ready documentation.
Enclave Strategy
Scoped compliance approach to isolate CUI systems and reduce complexity and cost.
Continuous Monitoring
Ongoing monitoring, logging, and alerting to maintain compliance over time.
Audit Preparation
Support for self-assessments and third-party audits with documentation and evidence gathering.
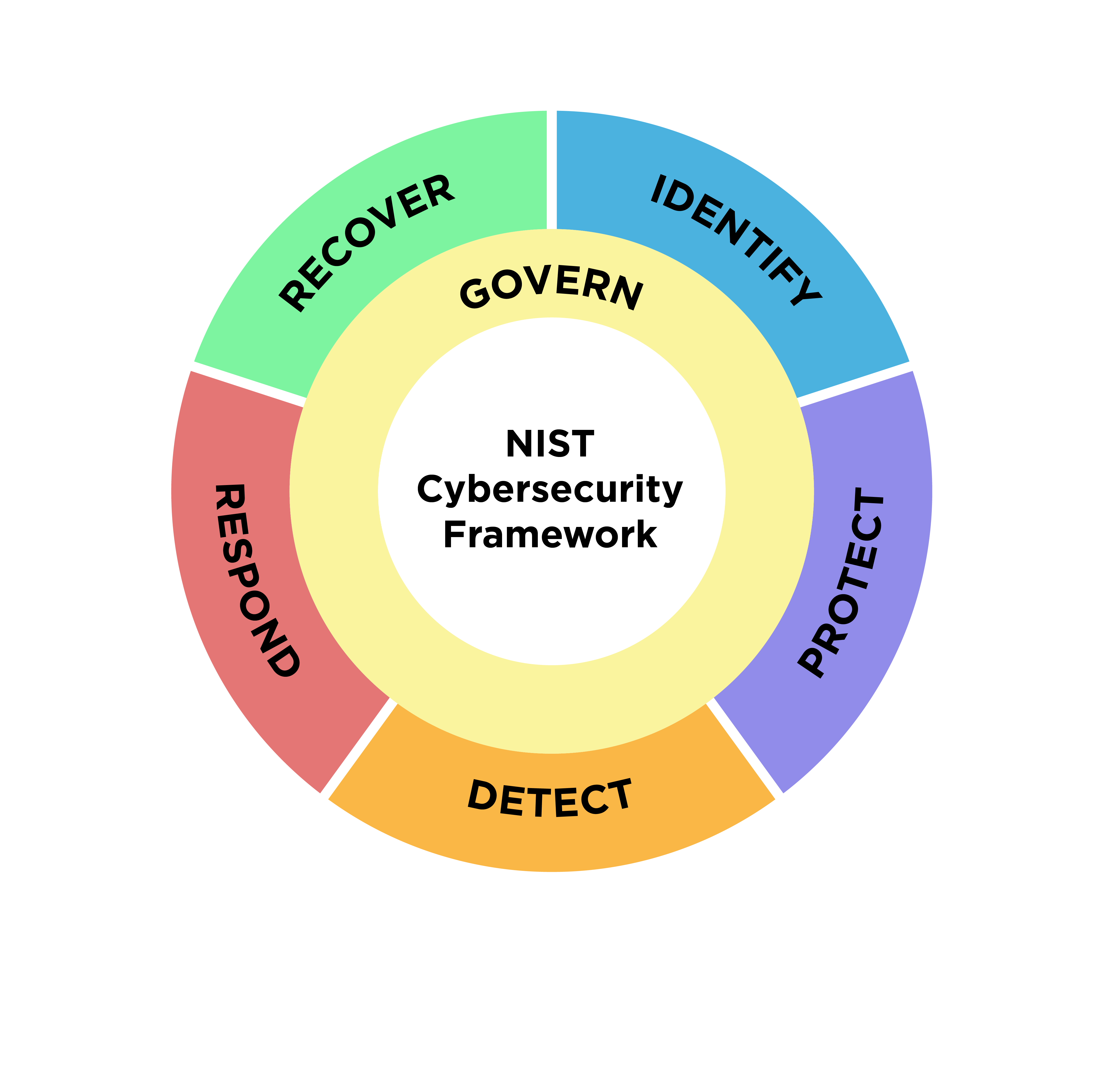
NIST Cybersecurity Framework
The NIST Cybersecurity Framework (CSF) provides a structured approach to managing cybersecurity risk. We align our security practices with the six core functions:
Govern
Establish cybersecurity strategy and oversight
Identify
Understand assets, risks, and vulnerabilities
Protect
Implement safeguards and access controls
Detect
Monitor for threats and anomalies
Respond
Take action when incidents occur
Recover
Restore operations after an incident
Zero Trust Architecture
Modern compliance frameworks increasingly require Zero Trust principles: never trust, always verify. We implement Zero Trust architecture through:
- Identity verification with Azure Entra ID and MFA
- Conditional Access policies based on user, device, and location
- Endpoint compliance enforcement with Microsoft Intune
- Network segmentation and micro-segmentation
- Least privilege access controls
Target Industries
- Defense Contractors (DoD)
- Manufacturing
- Engineering Firms
- Government Contractors
- Healthcare & Dental
- Financial Services
- Law Offices
- Accounting Firms
Ready to Address Your Compliance Requirements?
Schedule a compliance assessment to understand your current posture and develop a roadmap to meet your requirements.